Cyberattacks have really caught traction across the globe. And in 98% of cyberattacks, social engineering was the weapon (Source).
It’s an interesting method of duping someone. It might sound really technical and complicated, but it’s not. It can just be a simple interaction involving:
All this comes with an innate feeling that if you fail to do as suggested, something bad might happen. And that pressure actually pushes many people into falling for the trap instead of pausing and thinking about it.
But let’s accept it, we can’t stay alert all the time waiting to get duped on a random day. In fact, we go through many other urgent events that are genuine, so we take the socially engineered one for the same.
In this guide, I’ll tell you how to identify a social engineering attack when you encounter one to protect yourself from it. From now on, whenever an urgency arises, you’ll be aware enough to go ahead with your reaction or think for a moment.
KEY TAKEAWAYS
- Social engineering attacks are quite prevalent nowadays.
- They involve duping someone by trickery and psychological manipulation.
- All of them have some common features like a sense of urgency, unexpected or premature requests, and personal or emotional undertones.
- Try to look for mistakes or inconsistencies; attackers mostly fail to perform a perfect attack.
All human hacking attacks have one thing in common: a sense of urgency that pushes you to take some action immediately.
You might receive a message suggesting that something important will expire, break, or be lost if you don’t respond right away. Now, urgency in itself is not bad. Life contains real deadlines. But social engineering urgency often feels slightly theatrical. It pushes you away from reflection and toward reaction. A helpful reframe is this: anything truly important will withstand a moment of thoughtful pause. Giving yourself even five minutes to step back can restore clarity.
Sometimes you do get an idea that something is fishy. Things are progressing differently from how they usually do. It can be an exceptional event, but why take a risk? It can also be a social engineering attack.
For instance, let’s say a coworker suddenly says they need access to some sensitive info, but they don’t go through the usual system or email through the official channel. What they do is ask you on some random app or in a weird way. Or maybe a company or service you deal with all the time suddenly wants you to verify your identity in some totally different way than they normally would. That kind of stuff might not seem like a big deal at first, but it’s worth paying attention to.
The thing is, routines and processes exist for a reason. They’re not just there to be annoying or slow things down; they actually help keep everything secure, organized, and fair. So when someone is trying to skip around those normal steps or change things up without a clear reason, it’s not wrong or rude to pause and think about it. You’re not accusing anyone of anything bad; you’re just being careful and doing your job properly.
A really simple way to handle it is just to ask a calm, normal question like, “Hey, can we just do this the usual way?” You don’t have to be dramatic or suspicious about it. A simple question can sometimes clear things up immediately. If everything is legit, the person will usually have no problem going back to the normal process. But if something is off, that question alone can expose it or at least make you rethink what’s going on.
The cyberattackers employing phishing won’t come off as aggressive strangers to you. In fact, they’ll take up an exact opposite personality.
They might lean into emotions in a really subtle way, like:
You might get a message that flatters you a bit, like saying you’re the only person who can help, or they might play on your kindness by making it sound like they’re in a tough spot and really need you. Sometimes it even feels a little personal, like they somehow “get” you or are reaching out genuinely. And that’s exactly why it works so well; it doesn’t feel suspicious at first. The tricky part is that none of those things is bad on its own. Being kind, empathetic, and willing to help people is actually a really good thing. You don’t want to lose that or become cold or paranoid just because of a few bad actors out there. But what does help is adding a tiny extra step to how you normally respond.
Instead of immediately acting on that feeling, you can pause for a second. It’s okay to feel sympathy or excitement right away; that’s just being human. But then, right after that, just take a moment to double-check things. Ask yourself two things:
It’s not about overthinking everything, just doing a quick reality check. A simple way to think about it is: feel first, then verify. You don’t have to shut off your emotions, just pair them with a little bit of awareness. That way, you can still be the kind of person who helps others and shows up with good intentions, but you’re also protecting yourself at the same time.
Whether due to limitations or their mistakes, social engineering attackers fail to perfect the attack most of the time. It can be:
It’s tempting to dismiss these as trivial, and sometimes they are. But your intuition is remarkably good at noticing patterns. When something feels “off,” even in a small way, it’s worth honoring that perception. You don’t have to jump to conclusions; simply slow down and take a closer look. Think of it less as suspicion and more as attentiveness.
Lastly, another signal of a human hacking attack can be a premature request for information that was due but to a later time. Maybe you’ve barely started talking, or the situation hasn’t really been explained properly yet, and suddenly they’re asking for things like your:
It can feel a little random when you actually stop and think about it, but in the moment, it might not seem that weird, especially if everything else about the conversation feels normal.
The thing is, most genuine interactions don’t jump straight to that kind of request. Usually, there’s a bit of a build-up. You get some context, you understand who you’re dealing with, and there’s some level of trust or verification first. It kind of happens naturally over time. So when someone skips all of that and goes straight to the “ask,” it can feel a bit rushed, even if you can’t immediately explain why. And that’s your sign to just pause for a second. You don’t have to react right away or say yes just because they asked. Taking a moment to think things through is completely okay. A really simple habit that helps is asking yourself something like:
If the answer is no—or even just “hmm, not really” that’s probably your cue to slow things down a bit. Maybe ask a few more questions, or go back to the usual process, or just wait until things make more sense. It’s not about being paranoid or difficult; it’s just about moving at a pace that actually feels right and safe.
The following infographic summarizes all the signs of social engineering attacks:
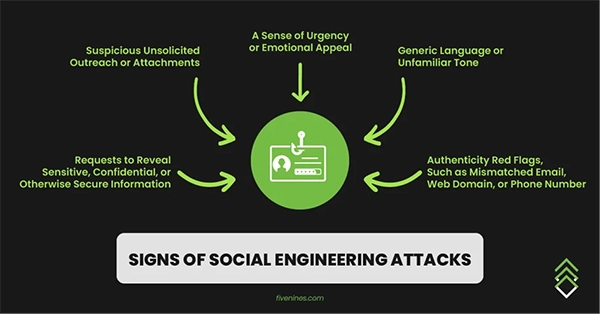
Just being simply a little more aware and alert can save you from social engineering attacks, as you’d immediately spot the above-listed signals.
It’s not about memorizing a bunch of rules or constantly trying to spot something suspicious in every little interaction. It’s more like having a sense in the back of your mind that helps you notice when something feels a bit off or out of place. And the important part is you don’t have to become super guarded or cynical to stay safe. You don’t need to start assuming the worst about people or questioning every single message you get. That’s not the goal at all. If anything, it’s kind of the opposite. The idea is to keep being your normal, open, kind self, just with a little extra awareness layered on top.
Don’t lose your trust in people, just balance it with a bit of thoughtfulness. You still help, you still respond, you still connect with others the same way you normally would. You’re just a little more tuned in to how things are happening and whether they make sense. It’s also really worth remembering that most of the interactions you have every day are completely genuine. The majority of people you talk to, whether it’s coworkers, friends, or random strangers, are just doing normal, honest beings. People, overall, are generally good. A few weird or deceptive situations don’t change that bigger picture.
Social engineering is often called “human hacking” and “confidence trick”.
Some common human hacking red flags are: artificial urgency, fear tactics, unexpected or premature requests for sensitive data or clicking on suspicious links.
Whenever there is a sense of urgency embedded in a request, most probably it’s a phishing attempt.
