
As the use of smartphones has grown, worries about spying on mobile devices have escalated. There are numerous potential spies to be concerned about. To begin with, there are online attackers like scammers, hackers, and others looking to steal your personal data.

When your smartphone starts acting weirdly, you can detect whether someone is watching through your phone. Performance problems, rising temperatures, decreased battery life, strange messages, strange sounds during calls, etc. are some indicators.
In this article, we will discuss how can someone track your phone and what to do if someone is spying on you.
You might be curious as to why someone would want to spy on your phone.. Knowing the motivations behind someone’s desire to hack or spy on your phone can help you stop it from happening.
Track Your Partner’s Android Phone
There are many advanced spyware apps for Android and iOS in the market. The most important question here is how to tell if your cell phone is being tracked, tapped, or monitored by the spy software. Fortunately, you can recognize the warning indications that could mean spyware is infecting your device and tracking your activities.
Here are 10 indicators that someone is watching you through your phone.
The most advanced spyware is concealed, but occasionally people abuse apps like parental control apps to eavesdrop on others. If someone is using one of these applications to spy on your phone, the spyware will be concealed.
Look through your phone for any new apps you don’t recall installing. Net Nanny, Kaspersky Safe Kids, Norton Family, and Qustodio are a few common ones to watch out for.
A spike in data usage could be a sign of mischief because the spy app requires data to send information back to the offender.
On an iPhone, select Settings and then Mobile Data to verify your mobile data. You can scroll down to see how much mobile data-specific applications are using, or you can view your overall data usage.

On Android, navigate to Settings > Network & Internet > Data consumption to view your mobile data consumption. The total quantity of cellular data used by your phone is displayed under Mobile. To see how your data use has evolved over time, tap Mobile Data Usage. Any new spikes can be found from this point.
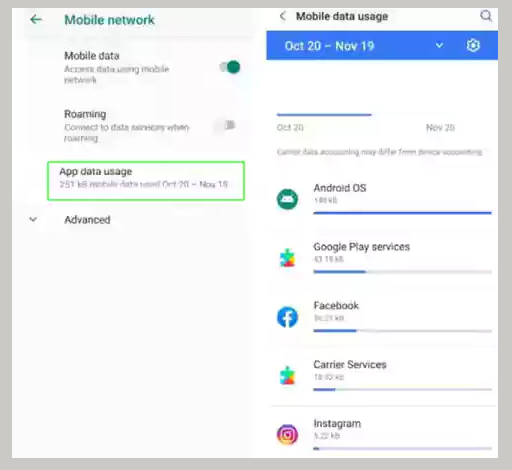
Once more, spyware is not always the cause of high data consumption. By examining each app’s data usage and usage patterns, you must first rule out genuine apps.
Users can load unauthorized apps without utilizing the official app stores via “rooting” an Android device or “jailbreaking” an iOS device. It’s a fairly strong indicator that something is wrong if you didn’t root or jailbreak your device.
Download the Root Checker software to determine if an Android device has been rooted. Look for the “Cydia” app on your device to see if an iOS device has been jailbroken.
When your phone is on standby (or sleep mode), it can still receive texts and calls, but it shouldn’t be producing any other sounds or lights. If so, malware might be the cause. The screen on your phone should be completely off when it is in sleep mode, not just dimmed.
Sometimes spyware apps can obstruct a phone’s shutdown procedure, causing the device to malfunction or take an abnormally long time to shut down.
Edward Snowden revealed NSA technology in 2014 that stops phones from completely shutting down so that they can be used for eavesdropping. Even though this is the outcome of a very sophisticated and carefully targeted assault, it shows that this kind of spying is feasible.

If your device is running hot, this could be an indication that spyware is being used to spy on you. This is particularly important if your phone continues to heat up even when you aren’t using it or using it sparingly.
Similar to this, spying may be to blame if your phone’s processing speed suddenly decreases. As more of your phone’s resources are devoted to the spyware program, it’s possible that its performance will start to suffer.

Your battery may discharge more quickly than normal if spyware is operating continuously. But since all batteries eventually deteriorate, watch for a significant and abrupt change rather than a decline over time.
Before concluding you have a problem, see if any newly installed or updated apps are to blame if you do observe a sudden change.
Keyloggers are a type of spyware that logs each key you hit. Your communications and login information could be recorded using a keylogger by someone monitoring your phone.
A malfunctioning autocorrect system is one indication that someone might be using a keylogger to eavesdrop on your phone. The autocorrect feature is affected by the keylogger, so if you observe it acting strangely or operating much more slowly than usual, someone may be monitoring your phone.
Malware and spyware can transmit and receive data through text messages. It’s probably a sign that something is wrong if you see texts sent by your account that you did not send.
Watch out for strange incoming communications as well. SMS messaging is occasionally used by primitive malware applications to connect to their server. If the message is connected to a spyware application, it will usually be coded in some way.
Strange background noises and unstable connections were common in the era of analog mobile phone networks. The all-digital mobile networks of today, however, typically offer connections that are reliable and largely noise-free.
There is a chance that someone is listening in on or recording your discussion if you hear odd noises in the background.
You need to act right away to get rid of any spyware you think is present. Learn what to do if someone is spying on you.
Using Antivirus software made for the purpose is the simplest approach to get malware from your phone. Your device will be scanned for spyware.
Use only software from well-known security companies because unknown security programmes could be infected with malware.
Change your credentials right away from another device whenever you have grounds to suspect spyware is jeopardizing your privacy. Otherwise, hackers can simply use spyware to obtain your new credentials.
Updates contain vital security fixes that prevent malware from abusing flaws. An updated system can stop spyware from operating correctly, and an updated antivirus can identify the most recent cyber threats.
Your accounts’ access protection is strengthened by 2FA. 2FA mandates that you use a different means to verify your identity in addition to your password. It’s a number typically sent via text message or email.
Resetting your phone to factory settings is your last resort if you find yourself up against an especially resilient spyware. All of your files, accounts and data will be deleted from your device during that procedure. Furthermore, it will remove all spyware applications.
Normally, I’d advise making a backup before performing a complete factory restart, but you might unintentionally back up spyware remnants.
The greatest offense is defense! You should therefore discover how to safeguard your phone against spyware.
It can be difficult to determine if someone is spying on your phone, but there are a few red flags you should watch out for.
Spying can also be done through different channels. Many covert actors, including your ISP, frequently monitor your internet activity. To safeguard your privacy and prevent internet activity tracking, you should use a private browser and a mobile VPN.
Now you can easily follow the tips mentioned above to stop someone from spying on your cell phone and safeguard your personal information.
Unfortunately, yes. On Android devices, apps may intercept your WhatsApp
communications, whereas it is not that easy on iOS devices due to the sandboxing security
of the operating system.
A person might be able to spy on you via a public Wi-Fi network if they have the
technological know-how and instruments required to intercept the data from your phone.
Your smartphone can be monitored by stalkerware (spyware), which can log your
location, and the websites and applications you use. Stalkerware can also capture all
keystrokes you make on your phone, which enables it to capture all text you type, including
emails, login credentials, and text messages.
