“Most of the security failures don’t start with hackers or break-ins – they start with outdated systems that quietly perform their jobs just enough to avoid attention”.
In today’s digital landscape, access control is more than a lock and a list – it’s identity, policy, telemetry and audit trails merged into one platform. As companies go hybrid, regulations get stricter and attackers get more advanced – an outdated access control system can be the main source of failure for security, compliance and productivity.
The good news – these failures can be altered just by partnering with an access control company and by understanding what your business is demanding with the evolving security landscape.
Go through the article that shares the reason for the requirement change, the seven clear signs that indicate upgrade demands, the real cost of ignoring this and a practical workflow to budget and grow with ease.
Two major pillars of the modern access control system are – the evolution of cloud/’Access Control as a Service’ models and the spread of hybrid models. Cloud and managed access control services are growing fast as businesses want remote management and quick feature upgradation. (Source – markets and markets)
Along with this, employees follow irregular schedules in hybrid models, so access rules need to be dynamic and centrally managed. As distributed teams are becoming normal, ensuring the right security maintains the right pace without slowing down workflow.
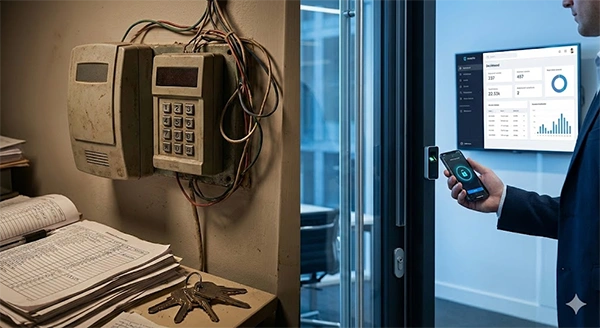
Access control issues barely happen overnight – they form quietly as businesses grow and operations change. What one worked well might slowly turn into security gaps, compliance risks and ineffective operations.
The following signs will let you know whether your current access control system is working fine or you need an upgrade:
If readers, controllers or management consoles are no longer supported by security patches and updates, then you are at risk. Think of it as driving a car with no recalls addressed – eventually, something will fail.
Unsupported systems are a compliance are a safety issue that often gets associated with ‘end of operating’ notices – do check yours.
Modern security is like an environment – access control should feed cameras, SEIMs and identity platforms. Disconnected systems slow down the investigations, increase the risk of false alarms and ignore audit records.
Modern access control must work as a single security setup to ensure visibility, accuracy and quick responses during emergencies. Get a better understanding with this case study –
CASE STUDY
A 120 person regional clinic used standalone badge readers and paper logs. Just after two closely missed incidents involving contractor access, they shifted to a cloud based access control system with mobile credentials and real time alerts.
The result – a 70% drop in unresolved badge issues, audit ready logs for regulators and centralized admin access that lowers almost half of the management time.
This shows how a thoughtful upgradation of the running issues of a company can result in smooth operations and efficiency.

Is your phone helping you to create time-limited visitor badges? Deny contractor access instantly? If not, you are left out of role-based controls. Manual spreadsheets and key lists are replaceable with policies that automatically enforce least privilege and reduce human errors to a great extent.
If unauthorized access attempts have become very common in your working environment – an upgrade is overdue. Incidents elevate costs across investigations, downtime and reputational damage – and the overall financial effect of security incidents continues to grow.
According to the IBM Cost of a Data Breach 2024 report, the average global breach cost has touched USD 4.88 million – a significant increase from the previous year.
If IT teams are on-site to change access rules, your system is not ready to move into this era. Modern technologies allow admins to push policy changes from anywhere, onboard remote employees and issue mobile credentials – important when the employees work off-site or require temporary access.
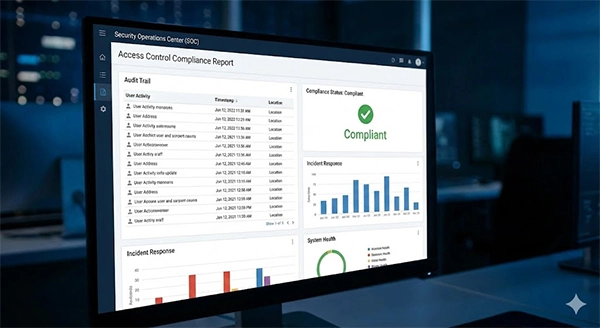
Regulated industries such as healthcare and finance need to have proof of who accessed what and when. Also, if your audits demand long manual reconciliations, you are lacking the reporting and chain-of-evidence your auditors expect. Upgrading turns compliance demonstrable and far less painful.
For guidance on controls and auditing, go through frameworks such as NIST SP 800- 53 (NIST Computer Security Resource Center) for authoritative references.
If every created site requires a forklift upgrade to install controllers, the system will possibly not scale. Modern architectures support edge controllers, multi-site management and cloud provisioning so that growth doesn’t mean exponential cost.
Delaying is always expensive. Beyond the obvious security risks, regulatory fines and operational inefficiencies accumulate. The rising average cost of data breaches – now in millions globally – shows how expensive modern incidents can be. Delays also turn future migrations harder and more costly – because technical debt compounds.
Planning an access control upgrade isn’t about selecting a new technology – it’s about ensuring the investment fits your operations, future plans and security demands. Here are the right planning and budgeting considerations that will help you modernize your business without unnecessary overspending-
Upgrading access control is a strategic step. If you are overwhelmed, choose a focused step – look up vendor comparisons, ACaaS pricing models and integration compatibility (directory, VMS, SIEM). For market and industry insights, browse reports from market analysts referenced above to build a shortlist and procurement checklist. And your go-to tech search engine can be GetAssist.
Upgrading is not a one time spend – it’s future proofing. Understand modern access control as the nervous system of your physical operations – when it’s healthy, everything moves with ease and with far less friction.
If two or more of the seven signs above describe your environment, take it as an urgent task to upgrade – before that ‘one badge’ turns into the story of a breach report.
If it lacks the remote management, real time access varies or audit logs – it’s likely outdated.
No, it also means to improve compliance, operational efficiency and user management.
Yes, the cloud based systems allow access changes from anywhere, anytime.
